OX Research found a filename validation bypass that escalates a prior patched authenticated RCE into Zero‑Click Unauthenticated RCE (CVE-2026-28289), patched in FreeScout v1.8.207.
TL;DR
Urgent Security Alert: Just days after an authenticated RCE vulnerability in FreeScout was disclosed, researchers at OX Research identified a bypass that escalates the issue into a Zero‑Click Unauthenticated RCE. The vulnerability, now tracked as CVE‑2026‑28289, is patched in FreeScout v1.8.207.
If you are running any earlier version, you are vulnerable – even if you patched last week. Update immediately.
- Type: Remote Code Execution (Unauthenticated, Zero‑Click)
- Severity: Critical
- Affected Versions: All FreeScout versions up to and including 1.8.206
Overview
A few days ago, we published research detailing a FreeScout vulnerability that allowed authenticated attackers to achieve full system compromise via RCE – originally reported by Offensive.sa.
On the same day, we discovered a patch bypass that allowed us to reproduce the same RCE on newly updated servers, demonstrating how quickly incomplete fixes can be circumvented.
During our deeper analysis, we escalated the attack chain further — converting it into a Zero‑Click RCE. By sending a single crafted email to any address configured in FreeScout, an attacker can execute code on the server without authentication and without user interaction.
The maintainers responded rapidly and released a corrective patch in v1.8.207, which was assigned CVE‑2026‑28289.
This case highlights a recurring reality in vulnerability remediation: a patch release does not guarantee risk elimination.
Even mature, actively maintained open‑source projects can ship fixes that leave residual attack paths. Attackers routinely diff patches, probe fixes, and search for variant exploitation paths within hours of disclosure.
FreeScout is a popular open-source help desk and shared mailbox application. Built on the PHP Laravel framework, it lets organizations manage customer support tickets and team inboxes without subscription fees or third-party hosting.
FreeScout has 4K+ GitHub stars and ~1100 publicly exposed instances identified via Shodan. Laravel is even more widely adopted, with 83K+ GitHub stars and ~13K publicly exposed servers identified via Shodan.
Who is affected
Our investigation confirmed exposed FreeScout deployments across public health institutions, technology providers, financial services platforms, and news organizations.
We are intentionally withholding identifying details to avoid increasing risk to affected parties.
- Directly Affected: Any organization with a support email based on FreeScout
Impact
If exploited, this vulnerability could enable:
- Full server/system takeover
- Data exfiltration of helpdesk tickets, mailbox content, and other sensitive support/inbox data stored in FreeScout
- Lateral movement from the FreeScout host to other systems in the same network
Recommended actions
- Update FreeScout to v1.8.207 or later.
- Always disable AllowOverrideAll in the Apache configuration on the FreeScout server, – even on the latest and patched version.
Proof of Concept
The PoC starts at 1:28:
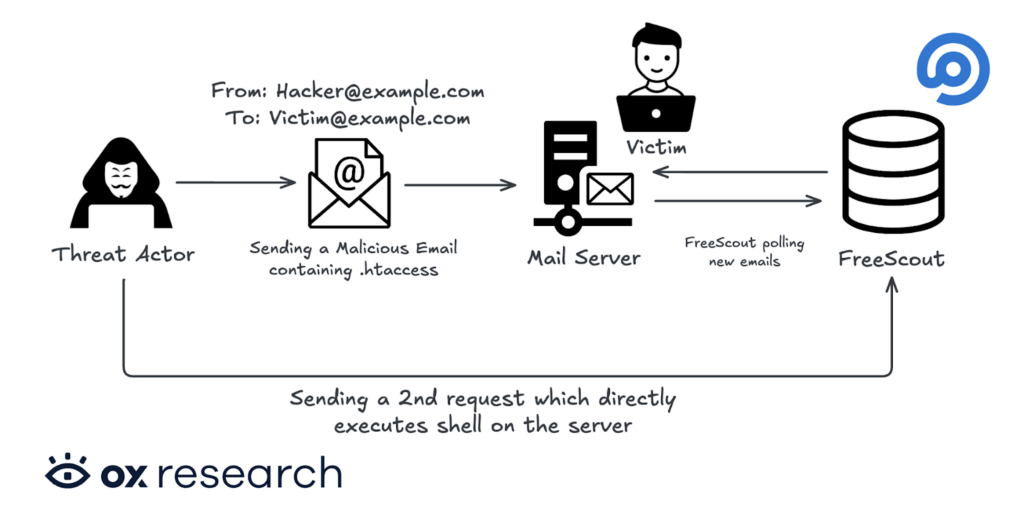
Attack Graph
Technical Analysis
While reviewing the patch for CVE-2026-27636 (covered in our previous blog post), we identified two issues:
- The fix is bypassable, and
- The original authenticated RCE chain can be escalated to unauthenticated RCE by sending a crafted email.
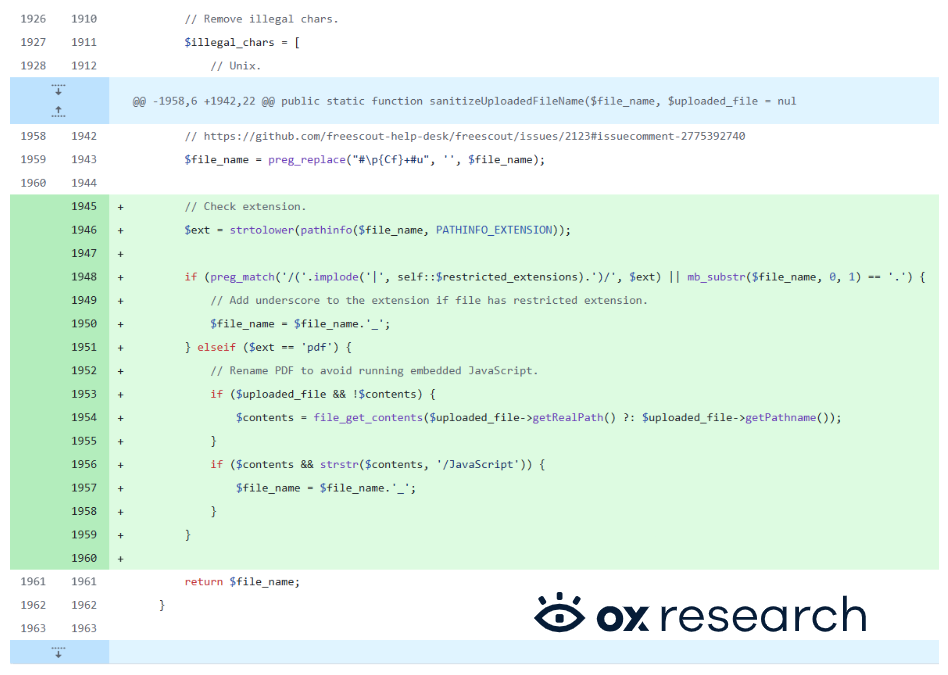
The prior fix attempts to prevent dangerous file uploads by appending an underscore to the file extension when a filename either uses a restricted extension or begins with a period (“.”).

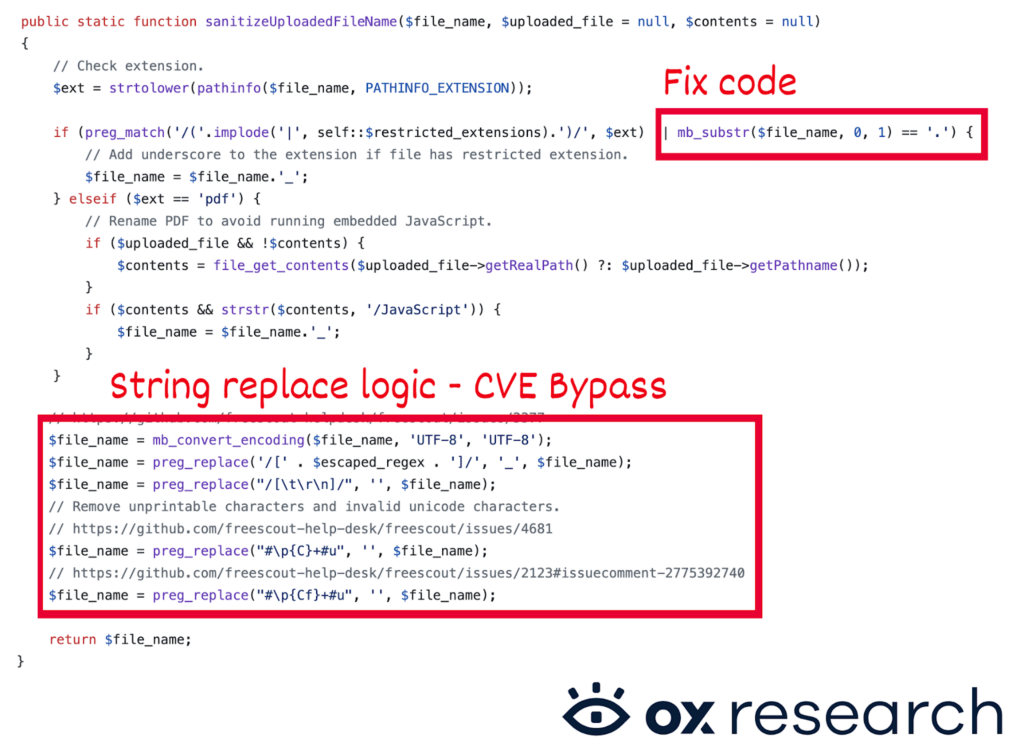
During code review, we found a way to bypass this filename validation by prepending a Zero-Width Space character (Unicode U+200B) to the filename.
Because U+200B is not treated as visible content during the initial check, it allows a filename to bypass the validation that blocks names starting with “.” Later in the processing chain, the U+200B character is stripped, causing the file to be saved as a true dotfile, despite having passed the earlier validation.
We responsibly disclosed the bypass to the maintainers, who addressed it in the following patch:
After confirming the bypass, we focused on escalating the original authenticated RCE into a fully unauthenticated remote code execution path.
The attack works by sending a malicious email from any address to a mailbox configured in FreeScout. Importantly, this requires no authentication and no user interaction. The malicious payload is written to disk on the FreeScout server and can then be leveraged to execute commands remotely.
The vulnerability is exploited by emailing the victim:
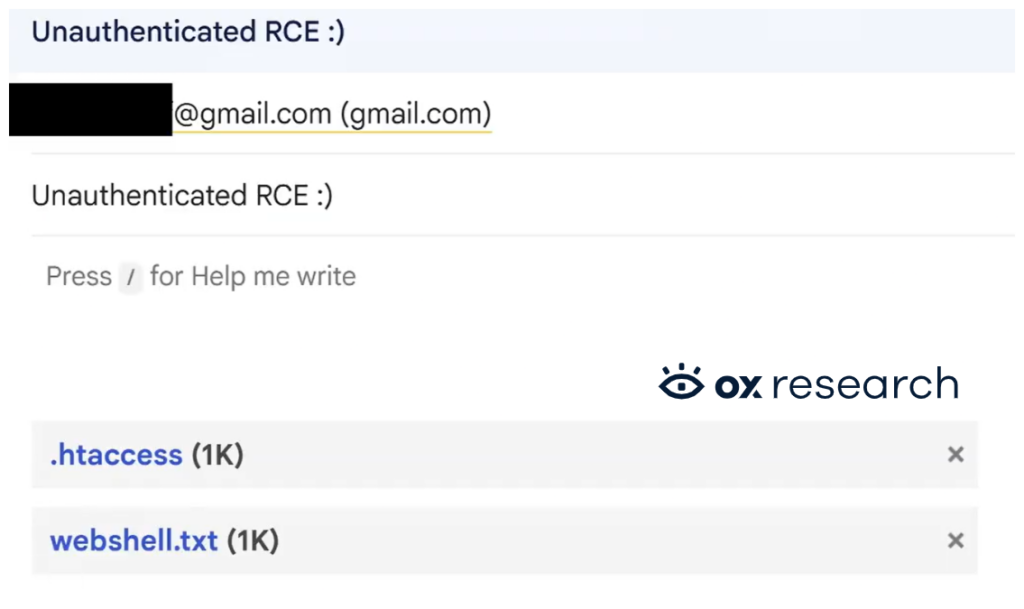
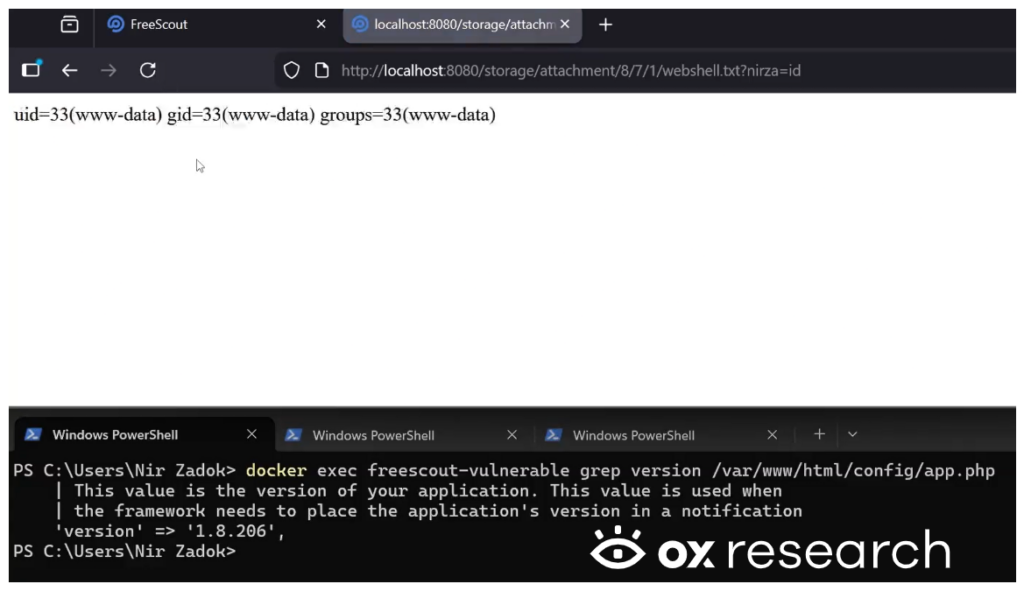
Subsequently, we can predict where the sent file is going to be saved when the email is received: “/storage/attachment/…”. Since we know where the files are being saved, we can access the payload on the server’s web GUI. By accessing it, the attacker gains the ability to execute commands on the server remotely.


)